ERC-2771 integration introduces address spoofing vulnerability — OpenZeppelin

Soon after Thirdweb revealed a security vulnerability that could impact a variety of common smart contracts used across the Web3 ecosystem, OpenZeppelin identified two specific standards as the root cause of the threat.
On Dec. 4, Thirdweb reported a vulnerability in a commonly used open-source library, which could impact pre-built contracts, including DropERC20, ERC-721, ERC-1155 (all versions) and AirdropERC20.
In response, smart contracts development platform OpenZepplin and nonfungible token marketplaces Coinbase NFT and OpenSea proactively informed users about the threat. Upon further investigation, OpenZepplin found that the vulnerability stems from “a problematic integration of two specific standards: ERC-2771 and Multicall.”
The smart contract vulnerability in question arises after the integration of ERC-2771 and multicall standards. OpenZepplin identified 13 sets of vulnerable smart contracts, as shown below. However, crypto service providers are advised to address the issue before bad actors find a way to exploit the vulnerability.
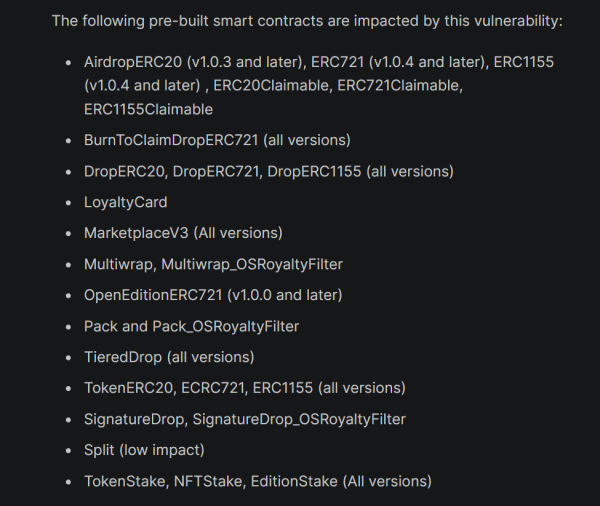
Smart contract vulnerabilities linked to ERC-2771 integration. Source: Thirdweb
OpenZepplin’s investigation found that the ERC-2771 standard allows overriding certain call functions. This could be exploited to extract the sender’s address information and spoof calls on their behalf.
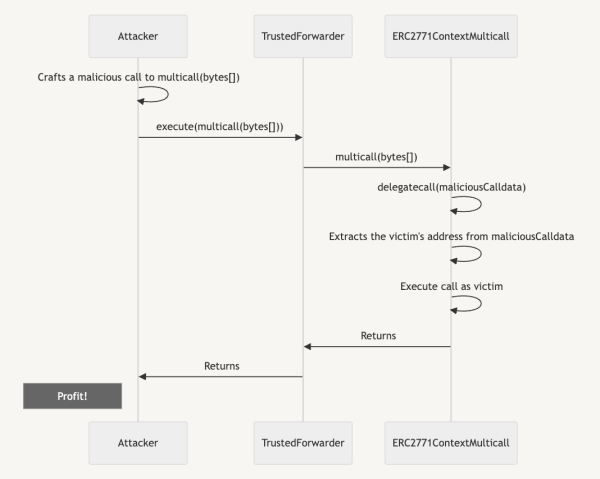
An attacker can potentially wrap multiple spoofed calls within a single multicall(bytes[]). Source: OpenZeppelin
OpenZepplin advised the Web3 community using the aforementioned integrations to use a 4-step method for ensuring safety: disable every trusted forwarder, pause contract and revoke approvals, prepare an upgrade and evaluate snapshot options.
In addition, Thirdweb launched a mitigation tool that allows users to connect their wallets and identify if a contract is vulnerable.
The decentralized finance platform Velodrome also deactivated its relay services until a new version was installed.
In a recent Cointelegraph Magazine article, experts revealed how artificial intelligence (AI) can help audit smart contracts and aid cybersecurity efforts.
James Edwards, the lead maintainer for cybersecurity investigator Librehash, said that while AI chatbots can develop smart contracts, deploying them in a live environment is risky.
On the other hand, Edwards highlighted the technology’s potential to vet smart contracts. Recent tests showed AI’s ability to “audit contracts with an unprecedented amount of accuracy that far surpasses what one could expect and would receive from GPT-4.”
While he concedes it’s not as good as a human auditor yet, it can already do a strong first pass to speed up the auditor’s work and make it more comprehensive.